-min.webp)
s businesses become more digitally inclined, they inadvertently expose themselves to cyber threats, turning cybersecurity from a discretionary measure into an imperative one. Small businesses, particularly, have become a favored target of cybercriminals due to their perceived vulnerability. While large corporations typically have established cybersecurity defenses, many small businesses are still catching up, leaving them exposed to various forms of cyber threats.
This guide will cover cybersecurity tips for small businesses to protect you from malicious actors.
Employee education and awareness
The role employees play in maintaining a business's cybersecurity cannot be overstated. Regardless of the strength of the hardware and software defenses, a company's security posture is only as robust as its least informed employee.
- Always check the URL: The most common hacking techniques aren’t complex hacking as depicted in the movies. It’s tricking people into giving up their information on websites and phone calls by impersonating a business, tricking people into clicking on malicious links, and other fraudulent behaviors. Checking the URL is essential for security.
- Use strong, unique passwords: When you use the same password for all your logins, more of your accounts are at risk when a breach occurs. Use a strong, unique password for every account.
- Use 2-Factor Authentication: 2-factor authentication (2FA, also known as multi-factor authentication) is an extra layer of security. So, even if someone knows your password, they also need your phone to prove they are you. You should never share your 2FA code.
- Update your devices frequently: The best way to stay updated on your devices’ security is to enable automatic software updates. This is usually available from the Settings or System Preferences app.
Secure network infrastructure
A secure network infrastructure is the backbone for any business's digital operations. It acts as the primary defense against external cyber threats and helps ensure that data remains safe and secure. Several key strategies contribute to building a robust and secure network:
- Robust firewalls and secure configurations: Firewalls guard against unauthorized access by monitoring network traffic. Secure configurations help reduce vulnerabilities and maintain proper access control.
- Software and firmware updates: Regular updates help patch security vulnerabilities in software and firmware, mitigating potential risks.
- Securing Wi-Fi networks: Strong encryption, like WPA2 or WPA3, and unique passwords help protect information transmitted over Wi-Fi networks. Consider a separate network for guests to secure your primary network further.
- Virtual Private Networks (VPNs) for remote workers: VPNs allow secure access to the business's network over the internet, protecting data transmission and allowing remote access to internal resources.
Data protection and backup strategies
Protecting your business's data is a multifaceted task designed to protect your business's most vital assets, promoting resilience and continuity, even in the face of unexpected cyber threats. Here's a brief explanation of the key strategies:
- Regular backups: Consistently back up essential business data to recover quickly from cyber-attacks or data loss.
- Secure cloud or off-site backups: Protect your data from physical damage using secure cloud storage or off-site backups.
- Encryption and access controls: Use encryption to secure data and implement access controls to ensure only authorized individuals can access it.
- Data breach response plan: Develop a plan to quickly respond and recover from potential data breaches, mitigating damage and restoring operations.
Regular security audits and updates
Regular security audits and updates are integral to a comprehensive cybersecurity strategy. Here are some strategies to identify potential vulnerabilities before they can be exploited and ensure that systems are protected against known threats:
- Conducting periodic cybersecurity audits: Regular audits help identify vulnerabilities and gaps in your security infrastructure. They assess your current security measures, identify weak points, and provide recommendations for improvement.
- Ensuring all software, applications, and systems are up-to-date: Regular updates are vital as they often contain patches for known vulnerabilities. Ensuring all systems are up-to-date minimizes the risk of exploitation.
- Monitoring and reviewing access logs and security logs: Regularly reviewing these logs helps detect unusual activity or breaches. If a breach occurs, logs can provide valuable information about the source and nature of the attack.
Vendor and third-party risk management
Vendors and third parties can pose a significant cybersecurity threat. Here's an overview of how you can manage vendor and third-party risks effectively to enhance your overall security posture:
- Assessing the cybersecurity practices of vendors and third-party partners: Since these entities often have access to your data or network, evaluating their cybersecurity measures is essential to ensure they meet your security standards.
- Implementing contractual agreements to ensure data protection: Include clauses requiring vendors to adhere to specific security practices in your contracts. This can protect your business and your data from potential security lapses on their part.
- Regularly reviewing and updating vendor agreements: Regular reviews and updates ensure your vendor agreements reflect current best practices and regulatory requirements.
Incident response and recovery
Effective incident response and recovery help you mitigate the impacts of a cybersecurity incident and strengthen your defenses against future threats.
- Establishing an incident response plan: This outlines the steps to take when a security breach occurs, minimizing damage and aiding in quick recovery. It should detail roles and responsibilities, communication protocols, and recovery procedures.
- Identifying steps to take in the event of a cybersecurity incident: Clear, actionable steps help ensure a coordinated response to incidents. This could include identifying and isolating affected systems, communicating with stakeholders, and initiating recovery processes.
- Conducting post-incident reviews and implementing improvements: After an incident, it's crucial to conduct a post-mortem where you analyze what happened, identify lessons learned, and implement changes to prevent a recurrence.
Cybersecurity insurance
Cybersecurity insurance can provide a financial safety net in case of a cyber incident. While cybersecurity insurance does not prevent cyber incidents, it can provide critical financial protection, helping you recover more quickly and efficiently when incidents occur.
- Considering cybersecurity insurance as an added layer of protection: Breaches can still occur despite your best security practices. Cybersecurity insurance can cover data breaches, network damage, and business interruption losses, reducing the financial impact.
- Evaluating coverage options and understanding policy terms: Cybersecurity insurance policies vary significantly. It's important to thoroughly understand what is and isn't covered, including specific cyber events, deductibles, and coverage limits.
Ongoing staff training and awareness
Continuous education and promoting a culture of awareness and responsibility can transform employees from potential security risks into cybersecurity defenders. Here’s how you can accomplish this:
- Encouraging continuous education on evolving cyber threats: Cyber threats continually evolve. So, it's vital that employee training does, too. Regular sessions should be held to educate staff on the latest threats and how to respond.
- Promoting a culture of cybersecurity awareness and responsibility: A culture that prioritizes cybersecurity helps ensure everyone understands their role in maintaining security. Encourage employees to follow best practices and maintain vigilance when handling sensitive information.
Next steps in cybersecurity protection
Cybersecurity has become a non-negotiable aspect of modern business operations, particularly for small businesses, which often face an elevated risk of cyberattacks. Cybersecurity is not just about safeguarding the business's operations. It's also about protecting customer data. In a time when data breaches are all too common, maintaining strong cybersecurity measures can enhance customers' trust and the business's reputation.
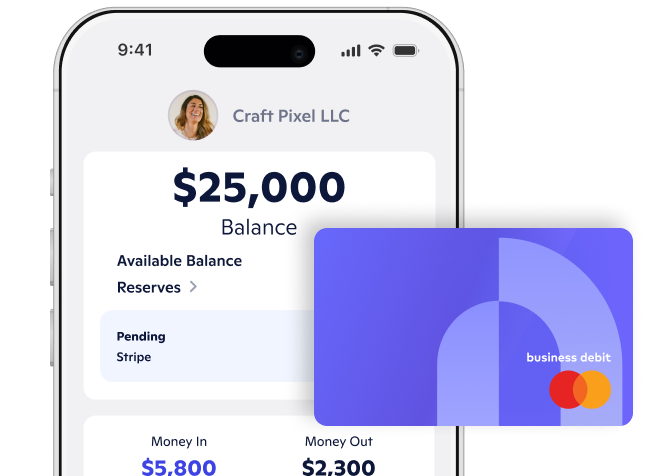
In this ever-evolving digital landscape, where threats are increasing in both sophistication and frequency, no business can afford to overlook the importance of cybersecurity. By taking a proactive, comprehensive approach, small businesses can protect their operations, build customer trust, and ensure their long-term success in the digital arena. With our industry standard safeguarding and security measures, Novo’s business banking can help keep your financial records secure.
Novo Platform Inc. strives to provide accurate information but cannot guarantee that this content is correct, complete, or up-to-date. This page is for informational purposes only and is not financial or legal advice nor an endorsement of any third-party products or services. All products and services are presented without warranty. Novo Platform Inc. does not provide any financial or legal advice, and you should consult your own financial, legal, or tax advisors.
Novo is a fintech, not a bank. Banking services provided by Middlesex Federal Savings, F.A.: Member FDIC.